PSA. RMM. ZenContract.
The Essential MSP Stack
Contracts that run your business, not sit in a folder.
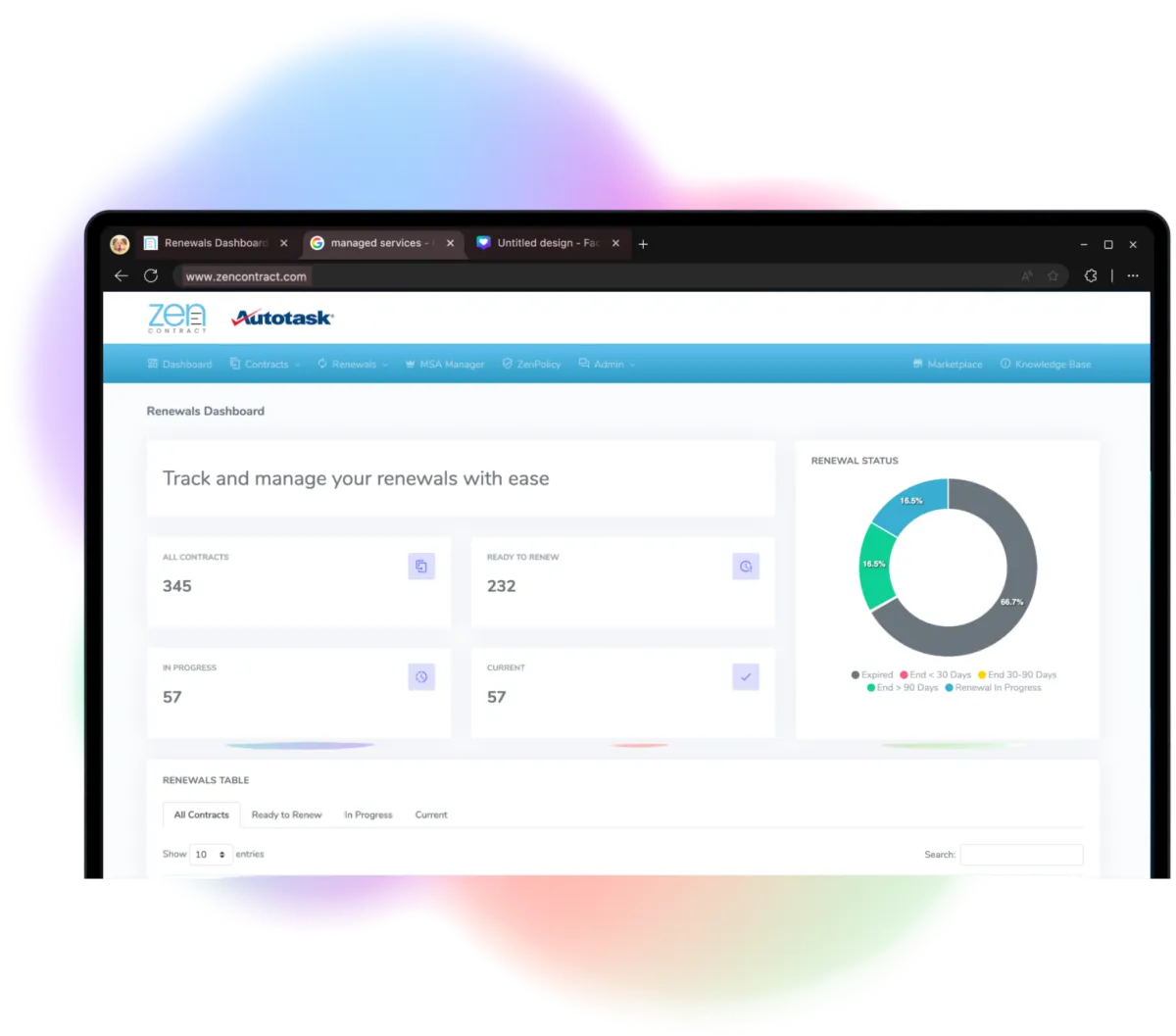
Your contracts, in sync with your PSA



Still losing hours to contract admin?
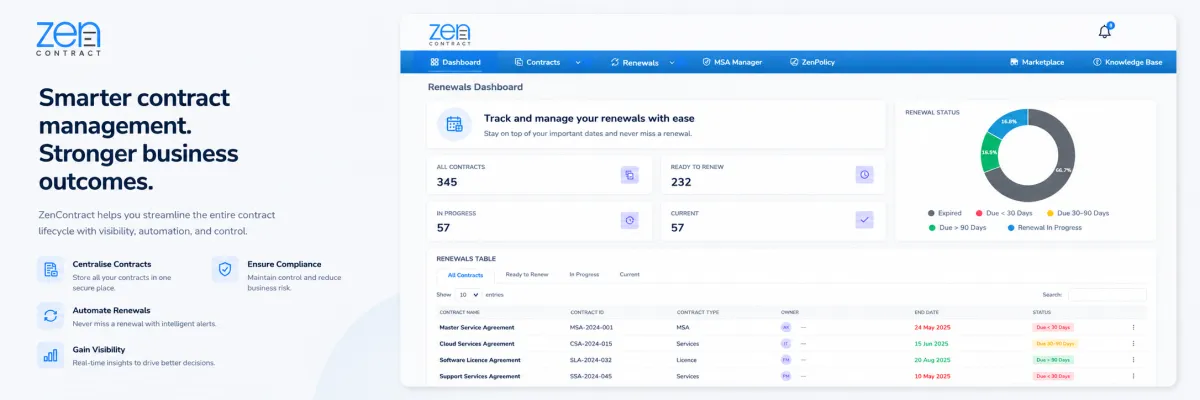
The Platform
Keep contracts, services and billing aligned across your MSP.
Set your process once.
Let it run.
Approval rules, automated CPI, renewal reminders and PSA sync all configured to match how your business operates.
ZenContract handles the workflow so your team can focus on the work.


Total control. Reduced risk.
Centralise all contracts, templates and pricing in one platform for complete visibility.
ZenContract prevent scope creep, revenue leakage and compliance issues, while giving you real-time oversight of every agreement.
Not ready for a full platform yet?
You can purchase professionally drafted MSP agreement templates without a ZenContract subscription.

Beyond the Platform
On Demand Legal Support
Practical advice, drafting and contract reviews when you need it.
Expert MSP Business Coaching
Hands-on guidance to improve how your business runs.

Giving you real-time oversight of all agreements and risk exposure.
Quick Links
Resources
© 2026 ZenContract. All Rights Reserved.